
A malware campaign is using a decoy Word document to automatically download an exploit-laden file and install a remote administration tool (RAT) for nefarious purposes.
SANS Internet Storm Center (ISC) Handler Xavier Mertens first spotted the attack at the beginning of October 2017.
The trouble begins when a user receives an attack email with an attached Word document. That file is different than attachments seen in other attack campaigns in that it has the OpenXML format and doesn’t contain malicious macros.
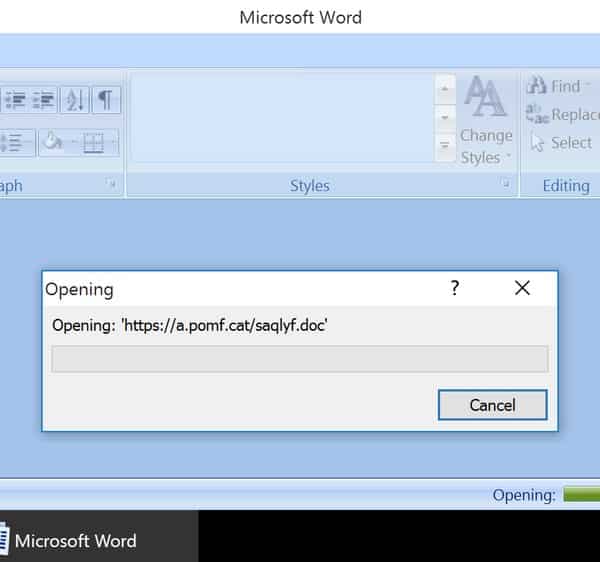
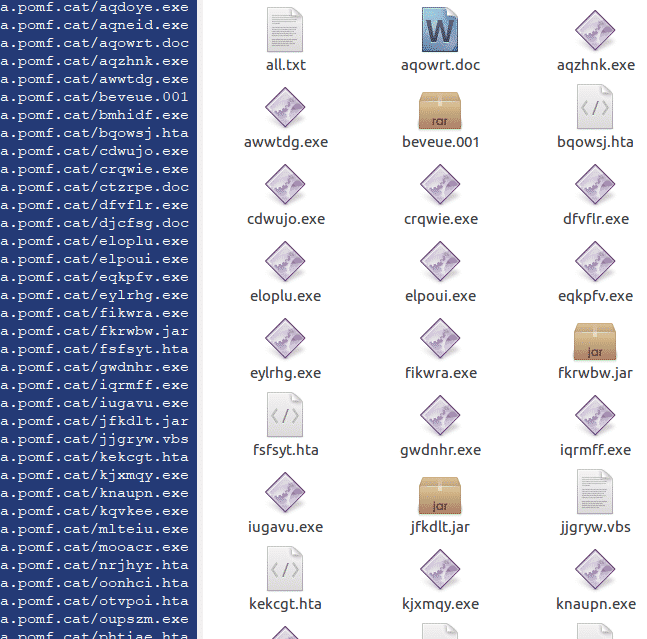
Included in the OpenXML of the attachment is a link to an external URL pointing to another Word document hosted at https://a[.]pomf[.]cat/saqlyf[.]doc. A closer look at pomf[.]cat reveals the domain to be the home of a free file hosting service that, among other things, appears to host a number of other malicious files.
So how is this external document liked to the attack email? Malwarebytes lead malware intelligence analyst Jérôme Segura has the answer:
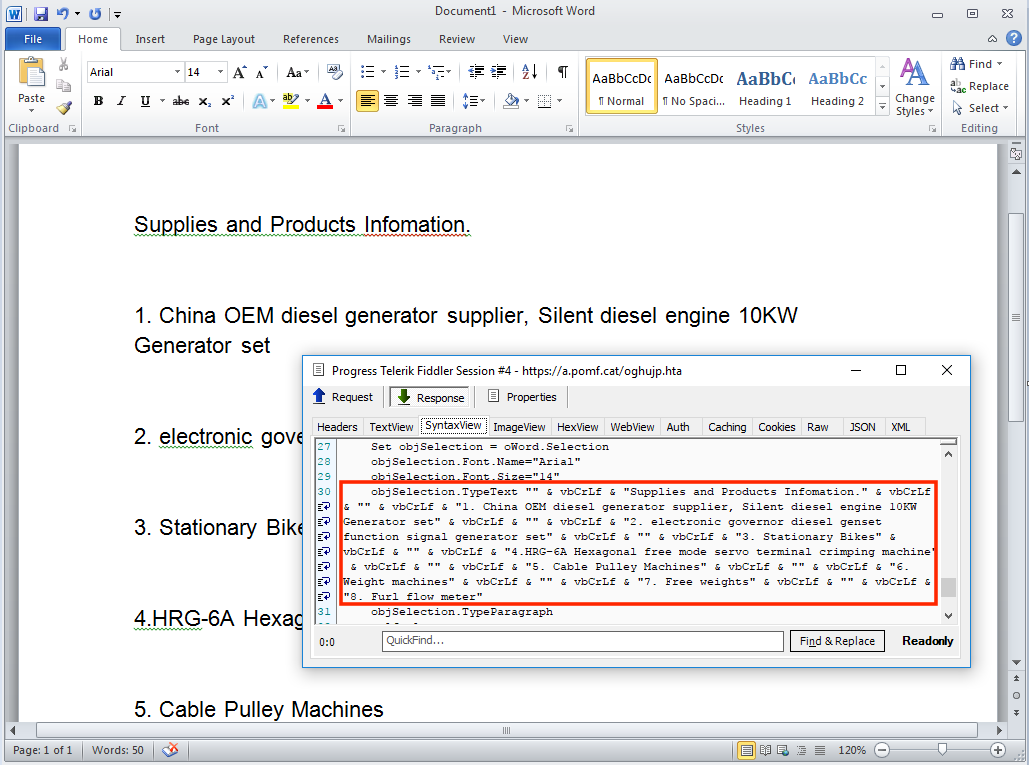
“In this case, the unsuspecting user opening the decoy Word document will trigger an automatic (no click or interaction required) download of a malicious RTF file that deploys an exploit (CVE-2017-8759), which ends up distributing the final malware payload.”
As you might recall, Microsoft patched the CVE-2017-8759 zero-day in September 2017. But that doesn’t mean admins and users have implemented the fix. Indeed, these malware attackers are banking on the fact that many computers have not received the fix and therefore can’t withstand installation of the final payload: a remote administration tool (RAT) known as Orcus Rat that bad actors can use for keylogging, grabbing screenshots, and obtaining remote desktop control.
While all of this is going on, the user sees a decoy document whose purpose is to convince them that all is well. Its remarkable number of misspellings should reveal that’s not the case, however….
No doubt the attackers used the benign Word document to evade detection and then push out the malicious RTF file. With that said, all organizations should make sure they focus on securing their endpoints. They should also make sure they have a robust vulnerability management program in place that can prioritize take care of zero-days on any vulnerable corporate machines.


