
The developers of the Petya and Mischa ransomware have officially made their malicious software open to the public.
The “Ransomware as a Service” (RaaS) program launched on 25 July pays out distributors based upon how many Bitcoins they extort from their victims. If the distributor collects lower than 5 Bitcoins a week, they get to keep only 25 percent of the payments.
As they rake in more money, they get to keep a greater percentage. Those who scare users into paying a total of more than 125 Bitcoins a week get to keep 85 percent of their haul.
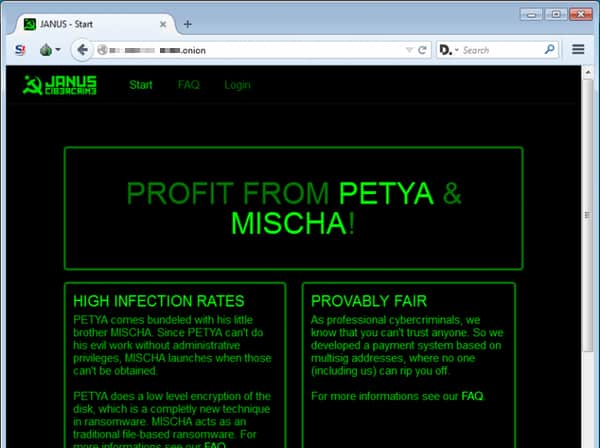
The developers of the RaaS program are also keen on attracting serious distributors only.
As security expert Lawrence Abrams explains in a blog post:
“Unlike other ransomware services, the Petya & Mischa RaaS requires potential affiliates to send in a small amount of bitcoins, which equates to ~$1.00 USD, in order to register. Though this is not a lot of money, the RaaS states it is being done to ‘discourage timewasters and kiddies’. They further state that this money will be refunded in the affiliates first revenue share payment.”
Petya first emerged on the crypto-malware scene back in March 2016. The ransomware requires administrative privileges to run so that it can replace the Master Boot Record and encrypt the Master File Table (MFT), which contains critical information about every file.

A single dropper is capable of installing Petya or Mischa onto a victim’s computer. If administrative privileges can be obtained, Petya will load up. If not, Mischa will infect the victim instead.
Unlike Petya, Mischa is a run-of-the-mill crypto-malware that encrypts a user’s files on an individual basis. It demands 1.9 BTC (approximately US $1240), which is considerably more greedy than Petya’s ransom of 0.9 BTC (US $590).
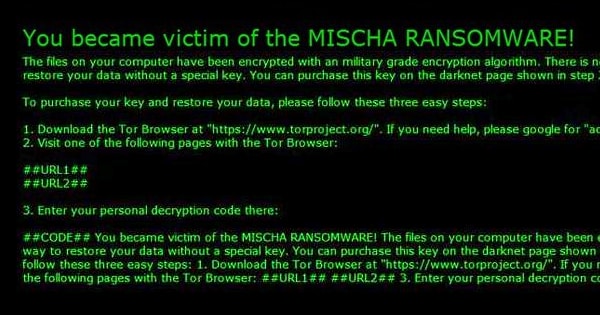
As of this writing, there is a decryption tool available for Petya ransomware but not for Mischa.
Users should therefore make an effort to protect themselves against a ransomware infection. That should involve keeping regular backups of their important data, installing a reputable security solution, and avoiding suspicious links and email attachments.


