There’s plenty of rumours and speculation, but one thing is certain: something has gone awfully awry with the computer systems at Sony Pictures Entertainment — the television and movie subsidiary of the huge Sony Corporation.
The media has been full since last week with reports that the company has shut down its servers, after a ghoulish skull appeared on computer screens alongside a claim that internal data had been stolen and would be released if undisclosed “demands” were not met.
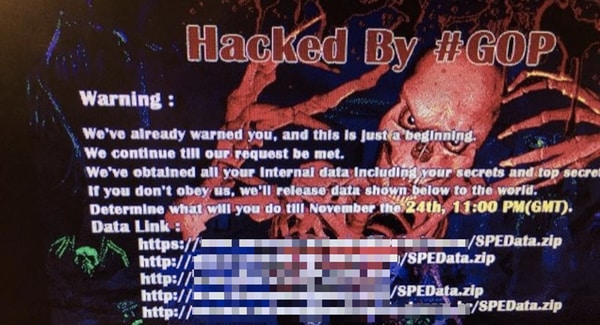
In parallel, Twitter accounts used by Sony to promote movies were hacked to display messages attacking Sony Entertainment’s CEO from a group calling itself GOP (the Guardians of Peace) who claimed responsibility for the hack.
Hacked by #GOP
You, the criminals including Michael Lynton will surely go to hell.
Nobody can help you.
James Dean, technology correspondent of the Times, reported that sources had told him that 11 terabytes of information had been stolen by hackers from Sony Pictures, and even tweeted a photograph of a sign placed in the lift of Sony Pictures’ London office asking staff not to use their computers or log into the WiFi.

“PLEASE DO NOT LOG ONTO YOUR PC EQUIPMENT OR COMPANY WIFI UNTIL FURTHER NOTICE”
If hackers have indeed hijacked Sony Pictures’ network, and stolen a large amount of data, it all sounds very dramatic, but the most the company has said publicly is that it is investigating an “IT matter.”
Quite frankly, from the outside, it’s hard to tell fact from fiction.
And the absence of hard facts about the hack has inevitably led to reporters filling in the vacuum with some guesswork and, in some cases, speculation that may be have shaky foundations.
For instance, one report claimed that Sony Pictures was exploring the possibility that North Korean hackers could be behind the attack – because of anger over an upcoming comedy film:
The timing of the attack coincides with the imminent release of “The Interview,” a Sony film that depicts a CIA plot to assassinate North Korean leader Kim Jong-Un. The nation’s ever-belligerent state propaganda outlets have threatened “merciless retaliation” against the U.S. and other nations if the film is released.

It does appear that North Korea is genuinely grumpy about the movie which stars James Franco and Seth Rogen, but does it really seem likely that that would motivate what appears to be a widespread attack against the Sony Pictures computer network?
An attack, lets not forget, that appears to have no qualms about drawing attention to itself (using ghoulish images of skulls, and calling out the Sony Entertainment CEO by name) but carelessly forgets to use the opportunity to praise North Korea’s supreme leader or call for the movie besmirching his image to be withdrawn.
That hasn’t, of course, stopped other media outlets from repeating the original claim of a North Korean link without much in the way of questioning, churning out the same “news” without considering just how tricky it might be to attribute the attack to any particular country – especially when the victim itself appears to still be mid-recovery and mopping up the mess.
Does North Korea use the internet to spy on other countries? I have no doubt. Is it possible that hackers sympathetic to North Korea (or simply people who aren’t fans of Seth Rogan) might want to disrupt Sony Pictures’ activities? Absolutely.
But it is hard to imagine that if the thing that raised the ire of the hackers was a movie about a CIA/Kim Jong-Un assassination plot that the hackers wouldn’t refer to either in their pronouncements.
And there are plenty of other groups whose feet Sony has trodden over the years, who could equally be speculated to have potentially been behind the attack. Is it not also possible that Celine Dion fans are still miffed that Sony BMG shipped a CD of her album which came with a rootkit pre-installed?
Possible, yes. But hardly likely.
And if I were a betting man, I’d wager that it was similarly fanciful that North Korea will be found to be the perpetrators of the current Sony hack.
Lets allow Sony Pictures to clean up its affected networks, and trust that they will inform consumers appropriately if any sensitive information has been stolen. My guess is that the computer crime-fighting authorities will have been contacted, and we should leave it to them to investigate who the perpetrators might be.
This article originally appeared on the Optimal Security blog.


