A piece of malware known as the Magala Trojan Clicker generates money by boosting advertisement click counts.
The threat, detected by Kaspersky Lab as Trojan-Clicker.Win32.Magala, fits in with the unloved Ask Toolbar and other such utilities as a type of potentially unwanted program (PUP).
Skirting the line between adware and malware, Magala doesn’t affect a user beyond co-opting some of their machine’s computing resources. But it does generate advertising revenue dishonestly and to the detriment of small businesses who pay for those advertisements.
Kaspersky Lab’s Sergey Yunakovsky has taken a close look at how the malware works, and shared his findings, including his observations covering the stages of a Magala infection, in a blog post:
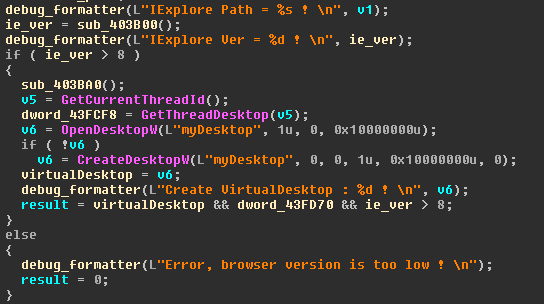
“The first stage of infection involves the Trojan checking which version of Internet Explorer is installed and locating it in the system. If it’s version 8 or earlier, the Trojan won’t run. So, if you still have this version on your computer, there’s nothing to worry about.”
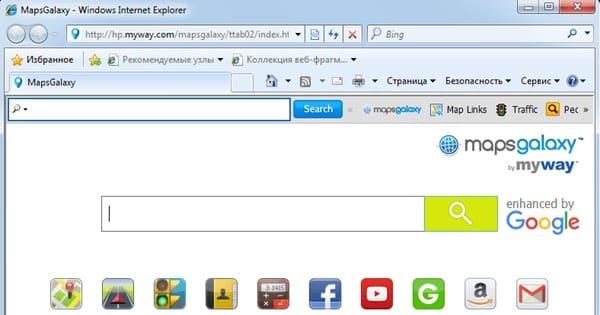
Assuming a later version of Internet Explorer is running on the infected machine, Magala creates a virtual desktop in the background. It then leverages IHTMLDocument2 to load the MapsGalaxy Toolbar, a program widely regarded as adware.
Once it’s confirmed the toolbar successfully installed, the malware contacts its remote server and retrieves a list of search queries that unscrupulous advertisers have slated for boosting. It then sends these queries and clicks on each of the first 10 links that appear in the search results at 10-second intervals.
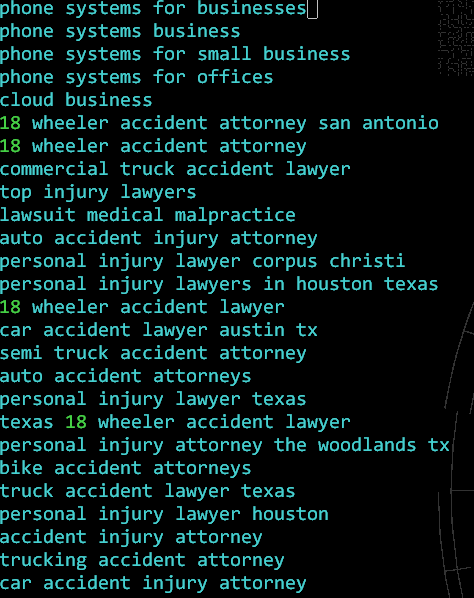
A campaign such as this typically generates about 7 cents per click, or about US $2.20 per thousand clicks. Such an amount is pittance when compared to what a botnet composed of thousands of enslaved devices could make. But it’s enough for unscrupulous advertisers to get up the next day and do it all again.
To protect themselves against Magala, users need to be think twice before they download a piece of free software somewhere on the web. Software developers don’t just build their programs for free. SOMEONE’s making money… the HOW just might not be obvious.
Users should also install an anti-virus solution onto their computers.