The Shlayer malware isn’t new. Two years ago when researchers discovered it infecting Mac computers they noted that the malware’s technique of disguising itself as an Adobe Flash Player update could hardly be considered novel either.
And yet, according to a recently-published report from Russian security outfit Kaspersky, there are now almost 32,000 unique variants of Shlayer and it accounts for a staggering 30% of all malware detected by the company’s Mac anti-virus products.
Perhaps even more stunning is another of the company’s statistics – that not only was Shlayer the most commonly-encountered Mac malware of 2019, but that it was seen at least once by 10% of users of Kaspersky’s Mac anti-virus products.
Can “one in ten macOS users” really have been attacked by Shlayer as Kaspersky claims? It feels remarkable if true.
One caveat, of course, is that many Mac users are still not running any anti-virus.
That means it’s possible that Kaspersky’s data is skewed because it is collated from Mac users who have chosen to run security software (and thus might consider themselves more at risk) or it might even mean that Kaspersky is actually *under-reporting* the true level of Shlayer activity because there is no insight on the computers which aren’t running an anti-virus.
Often Shlayer has been distributed via websites claiming to offer a live stream of a soccer match, software cracks, or posing as pirated episodes of popular TV shows. Unsuspecting users might have been directed to the sites by search engines, malicious links posted in YouTube video descriptions, or even the footnotes of Wikipedia articles.

Interestingly, Kaspersky’s research team says that the boobytrapped Wikipedia footnotes were not placed there by the malware distributors themselves:
“These links were not added by the cybercriminals themselves: we found that all those malicious domains had recently expired, and, judging by the WHOIS data, they now belong to a single individual. On the websites, the newly minted owner posted a malicious script that redirects users to Shlayer download landing pages. There are already over 700 such domains in total.”
Eventually, through whatever route, an unsuspecting user arrives at a webpage and sees the tempting content they wish to access. They click, and are greeted with a notification that they should install an update to Adobe Flash Player.
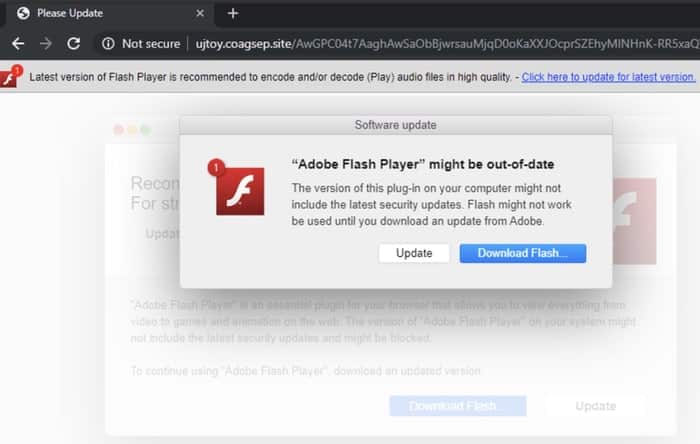
Of course, you should only ever download your Adobe Flash updates (if you wish to run it at all) from Adobe itself.
And although many Mac users have little need for Adobe Flash in this day and age, clearly Kaspersky’s research shows that there are many who will go ahead and install the malicious update, and compromise their Mac computer.
It’s a crude technique, but it works. And if the criminals are continuing to make money by infecting Apple Mac computers in this fashion, whatever makes you think that they’ll come up with a more original social engineering trick?
I advise all Mac users to run an up-to-date anti-virus program, and exercise caution about the software they install onto their computers.