
Hackers could exploit several flaws in the Panasonic Avionics In-Flight Entertainment (IFE) system to spoil an airline flight for their fellow passengers.
Specifically, actors could abuse the vulnerabilities to hack passengers’ in-flight displays and steal their credit card information. They could also potentially leverage those flaws to gain access to other systems if proper safeguards are not implemented onboard the plane.
Ruben Santamarta, principal security consultant at IOActive, explains that he came across the vulnerabilities in 2014:
“While I was flying from Warsaw to Dubai two years ago, I decided to try my luck and play with the IFE a little bit, touching this and that. Suddenly, after touching a specific point in one of the screen’s upper corners, the device returned this debug information:
Interactive: ek_seatappbase_1280x768_01.01.18.01.cram
Content: ek_seatappcontent_1280x768.01.01.8.01.cram
Engine: qtengine_01.14.0.01.squash
LRU Type: 196 2
IP: 172.17.148.48
Media Player Auto Popup Enabled: false“
A little research into those keywords after disembarking revealed hundreds of publicly available firmware updates for the Panasonic Avionics in-flight systems used by a number of airlines:
- Emirates
- AirFrance
- Aerolineas Argentinas
- United
- Virgin
- Singapore
- FinnAir
- Iberia
- Etihad
- Qatar
- KLM
- American Airlines
- Scandinavian
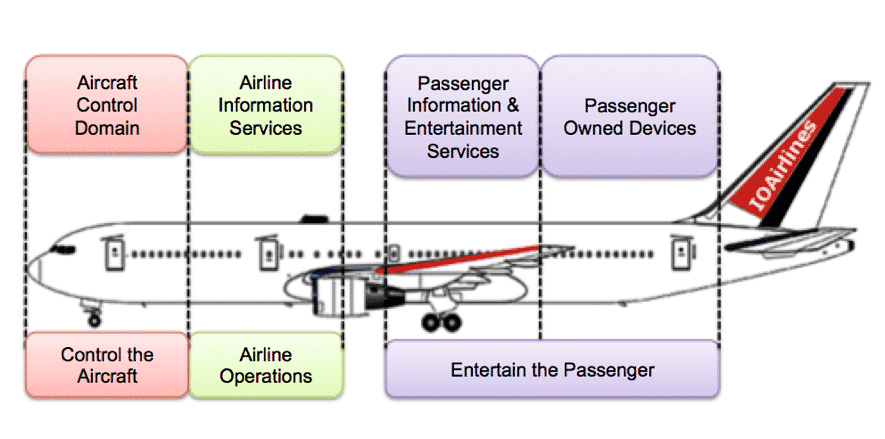
Like most IFEs, Panasonic’s system comes with a System Control Unit (SCU) located near the front of the plane that receives information about the flight (like temperature outside, latitude and longitude, and speed) from the avionics bus (or backend). It can then relate that data to the Seat Display Unit (SDU), a part of the IFE which passengers can use to watch movies, listen to music, and buy items using the SeatApp.
IFEs also come with a Cabin Crew Panel that allows flight attendants to control the lights and PA system using a CrewApp.

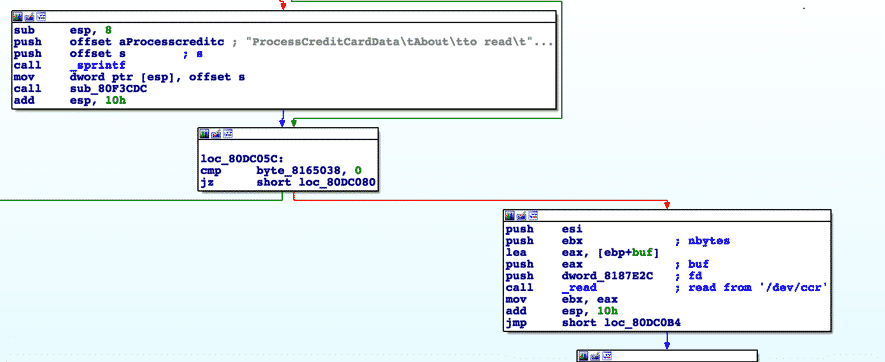
By analyzing the scripting language used by Panasonic’s IFE to extend and interface with the GUI and features of the main application, Santamarta found several vulnerabilities that if exploited would in most cases only cause passengers distress.
For example, attackers could spoof the plane’s flight information to convince them they’re going to another destination, that the plane is losing altitude, or that the temperature is unrealistically warm outside the plane. Alternatively, they could compromise the Crew Panel to mess with the lights and PA system.
That’s not all an attacker could do. The IOActive security researcher elaborates:
“The capture of personal information, including credit card details, is also technically possible due to backends that sometimes provide access to specific airlines’ frequent-flyer/VIP membership data.”
There is a bright side, though. Attackers couldn’t abuse the vulnerabilities to fly the plane sideways, as one security researcher claimed he did after hacking one of his flight’s IFE systems.
But just to be clear, that assumes the airline has taken certain precautions into consideration. Santamarta clarifies that point:
“Avionics should be located in the Aircraft Control domain, which should be physically isolated from the passenger domains; however, this doesn’t always happen. This means that as long as there is a physical path that connects both domains, we can’t disregard the potential for attack.”
The moral of the story?
Airlines need to make sure they segment their IFE systems from the rest of the plane. They also need to work with companies like Panasonic (like Santamarta did by practising responsible disclosure) to patch vulnerabilities as they arise.



Well this is extremely inaccurate. Your first sentence claims he could impact other customers, however he clearly could not even compromise his own seat. Ruben should try weaponizing something, instead of being a Chris Roberts.