An ambitious Android banking trojan can make off with almost any file on an infected device by achieving superuser rights.
Researchers at Kaspersky Lab first came across the malware, known as Trojan-Banker.AndroidOS.Tordow.a or “Tordow” for short, back in February 2016.
At first glance, Tordow behaves like other mobile banking malware.
An infection begins when a user installs a malicious copy of a popular app.
Is that any surprise?
Malware authors have long been using fake applications to disseminate their programs. Pokémon Go knockoffs are one of the most popular tricks to emerge in 2016, though other fake mobile games and even stopwatch apps also suffice.
To each of the fake apps malware developers have added some additional code that decrypts and launches a file.
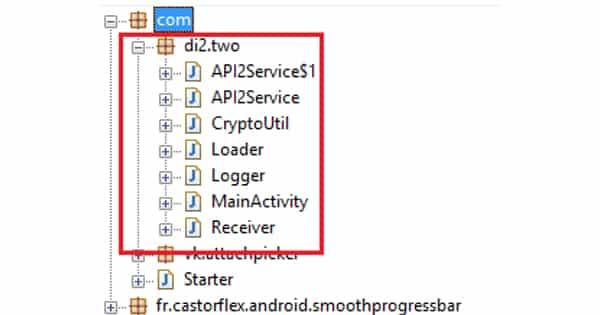
Kaspersky researcher Anton Kivva says it is at this point that Tordow reveals its modular design:
“The launched file calls the attacker’s server and downloads the main part of Tordow, which contains links to download several more files – an exploit to gain root privileges, new versions of malware, and so on. The number of links may vary depending on the criminals’ intentions; moreover, each downloaded file can also download from the server, decrypt and run new components. As a result, the infected device is loaded with several malicious modules; their number and functionality also depend on what the Tordow owners want to do. Either way, the attackers get the chance to remotely control the device by sending commands from the C&C.”
Those commands allow the malware to steal banking credentials via any number of means such as by intercepting SMS messages, stealing contacts, and removing applications.
But Tordow isn’t any ordinary banker.
At the time of infection, the trojan uses an exploit package to acquire root privileges. Those superuser rights enable Tordow to get up to all kinds of trouble.
For instance, it looks to see if the default Android web browser or Google Chrome browser is installed on an infected device. If so, it makes off with those browsers’ databases in an attempt to steal a user’s passwords, cookies, and (yes) *more* banking credentials.
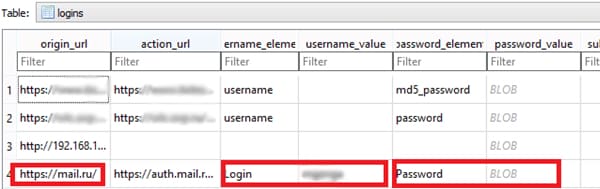
That’s not all, explains Kivva:
“The superuser rights make it possible to steal almost any file in the system – from photos and documents to files containing mobile app account data.”
Tordow is an ominous harbinger of things to come. Malware authors are getting much more sophisticated with their creations. As their capabilities improve, so too does their software.
Apparently, it wasn’t enough for Tordow to target people’s banking credentials. It has to also go after all of a victim’s information AND root their device.
Given threats like Tordow, it’s more important than ever for people to protect themselves against mobile malware. That includes installing an anti-virus solution on their devices, avoiding clicking on suspicious links and email attachments, and downloading apps only from the Google Play Store (or the App Store for Apple).


