
Researchers have released a free decryption tool for Jigsaw, the sadistic ransomware that gradually deletes all of a victim’s encrypted files.
Security expert Lawrence Abrams recently came across one variant of the ransomware, which asks victims to pay a ransom of US $150.
At this time, no one has confirmed how the ransomware is distributed. When it infects a user’s system, however, it targets 240 different unique file extensions, encrypts all relevant files with AES encryption, and appends a .FUN, .KKK, .GWS, or .BTC extension to them.
Here is the list of file extensions that the Jigsaw ransomware targets:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp , .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .c, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .Qbw, .QBB, .QBM, .QBI, .QBR , .Cnt, .Des, .v30, .Qbo, .Ini, .Lgb, .Qwc, .Qbp, .Aif, .Qba, .Tlg, .Qbx, .Qby , .1pa, .Qpd, .Txt, .Set, .Iif , .Nd, .Rtp, .Tlg, .Wav, .Qsm, .Qss, .Qst, .Fx0, .Fx1, .Mx0, .FPx, .Fxr, .Fim, .ptb, .Ai, .Pfb, .Cgn, .Vsd, .Cdr, .Cmx, .Cpt, .Csl, .Cur, .Des, .Dsf, .Ds4, , .Drw, .Dwg.Eps, .Ps, .Prn, .Gif, .Pcd, .Pct, .Pcx, .Plt, .Rif, .Svg, .Swf, .Tga, .Tiff, .Psp, .Ttf, .Wpd, .Wpg, .Wi, .Raw, .Wmf, .Txt, .Cal, .Cpx, .Shw, .Clk, .Cdx, .Cdt, .Fpx, .Fmv, .Img, .Gem, .Xcf, .Pic, .Mac, .Met, .PP4, .Pp5, .Ppf, .Xls, .Xlsx, .Xlsm, .Ppt, .Nap, .Pat, .Ps, .Prn, .Sct, .Vsd, .wk3, .wk4, .XPM, .zip, .rar
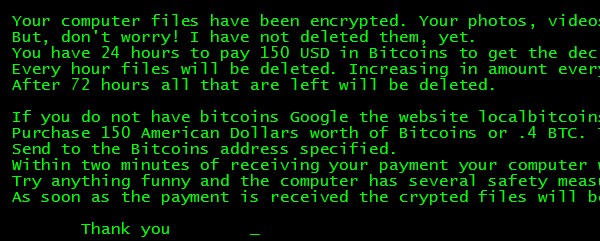
Once the encryption process is complete, Jigsaw makes itself known to its victim:
“Your computer files have been encrypted. Your photos, videos, documents, etc… But, don’t worry! I have not deleted them, yet. You have 24 hours to pay 150 USD in Bitcoins to get the decryption key. Every hour files will be deleted. Increasing in amount every time. After 72 hours all that are left will be deleted.
If you do not have bitcoins Google the website localbitcoins. Purchase 150 American Dollars worth of Bitcoins or .4 BTC. The system will accept either one. Send to the Bitcoins address specified. Within two minutes of receiving your payment your computer will receive the decryption key and return to normal. Try anything funny and the computer has several safety measures to delete your files. As soon as the payment is received the crypted files will be returned to normal. Thank you.”
There is a 60-minute countdown programmed into the ransom message. When it hits zero, one of your files will be deleted, and the timer will be reset. Only this time the file counter will increase, causing even more files to be deleted.
Try to shut down your computer? The ransomware will delete 1,000 files as punishment. Wait three days? Jigsaw will delete every last one of your files.
Abrams comments that the fact that Jigsaw goes through with its file deletion threats makes it unusual:
“It is not the first time that we have seen ransomware threaten to delete files, but this is the first time that one has actually carried out its threats.”
Fortunately, the security researcher along with @MalwareHunterTeam and @demonslay335 have come up with a decryption tool that allows victims to unlock their files for free.
Users affected by Jigsaw are urged to use Task Manager to terminate the firefox.exe and drpbx.exe processes and use MSConfig to disable the entry firefox.exe. These two steps will disable the ransomware’s startup and will prevent it from deleting any more files.
Next, they should download the Jigsaw Decryptor tool, found here, and use it to decrypt their files.
Finally, they should scan their computers for additional infections via an anti-virus solution.
Jigsaw is a unique ransomware variant. Not only does it actively delete a victim’s files, but for some variants, it expects little from its victims – sometimes as low as US $20 in payment.
As Abrams points out in his post, one cannot help but wonder: are the computer criminals behind Jigsaw actually interested in the money, or are they more invested in screwing with people? Those with nothing to lose are the most despicable form of attacker; they’ll do anything to cause their victims the most amount of distress.
Let us hope this decryptor tool continues to block the nefarious purposes of these bad actors, regardless of their motivations.



Or, you could just laugh and restore from backup.
If there is no sane backup strategy in place then there's clearly no data of value and the system can be wiped and re-installed. Either way, one move checkmate. Without requiring additional software.
Ofc, like any other problems, dealing with the symptoms is not as viable as dealing with the cause. Prevention is better than the cure.
It's actually alarmingly simple to prevent falling foul to such trickery.
Don't install it.
It really is that simple. Computers do not decide for themselves, whimsically, to do things. That requires more imagination than they are capable. Computers do as they are told. If you tell it to do something stupid, it'll do something stupid. You don't tell it to do anything it'll sit and wait until given instruction.
Although not a precise infection vector, it is direct consequence(every single case I've seen at least) of user action. Effects may become delayed in manifest in order to obscure quite when/what/how this is introduced to the system. But it is typically the direct consequence of the logged in user's actions.
Common ones include – but are not limited to;
– Clicking dodgey links in spam
– Navigating to untrustable websites whilst running rediculously easily exploitable operating systems and or softwares
– Installing softwares from irreputable sources – especially "cracks patches and keygens"
It's all easily avoidable – which is why it's only featuring on a small percentage of systems.
Ofc, this may be easier in a more secure environment. One where you actually retain some measure of control.
With regards to links in spam, and navigating to unsound areas of the interwebs then if you don't *know* this is something you can trust -=- Don't click it. Careless clicking costs lives. Instead consider validating trustability. Throw the link into a search engine instead, see what that pulls back. Try looking up the domain – see how long it's been active, last modified etc. Who owns it. Look them up n see what they are about.
A really good move would be to harden the browser by stopping it from executing random third party code as a default. For a physical analogy of executing third party code as default – which is at best insanity – consider a "suggestions box". But one where you impliment the suggestion regardless of who wrote it or how stupid the idea is.
This is kinda how your browser operates OOTB. Works well, as long as you only put sane suggestions in the box. When dealing with masses of random people it's most unwise to assume all suggestions to be sane. A better policy by far would be to assume all are insane and weigh them on their individual merit as they become applicable.
A common browser extension to provide such functionality would be noscript. Intended for various mozilla flavours of browser but as they're all running on the same extension system now it should work in others theoretically – else there's likely something similar available if the functionality does not natively exist. An incredibly simple, yet effective concept – Do not execute random code as default. Only execute code flagged as safe to execute. To save this from becomming detrimental to your browsing experience of your more regular haunts it's possible to whitelist by domain. You can apply temporary execution rights. You can grant execution rights to one specific object. Such an initiative alone will reduce the risk of a lot of potential issue.
Sandboxing is another good move. Some browsers attempt to impliment this, with lesser or greater degrees of success. I'd personally suggest the use of a virtual machine in order to create a distinctly seperate environment for the browser – it's own virtual computer it executes on. Preferably used for the browser exclusively. Anything goes wrong with the virtual machine then your actual hardware should remain unscathed. When you navigate to timsgianthairydildo.com and suddenly all it's files become encrypted you've just lost nothing but a disposable OS with a browser in it.
If you set the VM how you'd like it – then backup it's image – should anything happen that results in the VM not being how you'd like it restoration takes as long as copying that image back. And you don't lose uptime on the host system. Popular VM solutions include Virtualbox and VMware. I personally prefer Xen but this may be a little encombersome for many – especially if combined with SEL.
A VM(ideally a seperate one to which you use the browser in) is also a good testing ground for software you're unsure about. As it should have limited ability to impact operability of the host, or other containers.
Generally you can avoid most issues with software by simply only obtaining the software directly from the original vendor. This is even more important for operating systems. To view things from the "attackers" angle, what's the easiest way to get someone to install your virus? Package it in something you know they'll want to exectute. This is where cracks, patches and keygens come in. In the case of an operating system, it's easier to make that install in an infected state than it is to try and get your nasties in after. You can assuredly get it in before A/V then.
When there's a new – preferably expensive – software on the market then there's typically a flux of people who think the software is worth using, but not worth paying for. It's like shooting fish in a barrel with a tactical nuclear device. You can't miss. Just put your crap online and wait for them to come n eagerly snap it up thinking they are being cunning. Welcome to the botnet.
Unless you've some particular reason to trust the team involved with the circumvention then I wouldn't suggest it. Some are reasonably trustable within themselves but have simply made poor choices. For example instead of writing their own keygen they've used some shady packager to put the key generation algorithym into an executable – typically with a crappy repetitive electronic tune and some visual distractions. Oh, and embedded malware.
If you want to use software without paying for it – look at the world of open source. It's all free. If you want to do something it's a fair bet someone else has wanted to first. And there's at least one tool that's really good at it. As the source is open you can examine the how it works and what it does. If you have no programming skills or knowledge then don't worry there's many many bored geeks who'll rip it to bits to find out how it works. Or to steal bits of it for their own code – Which with open source is perfectly legitimate practices.
If there's something suspect in there – say hardcoded credentials allowing systemwide access – it's usually found. If it isn't fixed in a reasonable time frame then as the source is open you can just fork it, call it something else – pull out the suspect parts and everyone will switch over to that. Like when Open Office was sold to Apache. As it's open source the devel team just forked the last build before they sold it and called it Libre Office. Continued on as before.
To give a loose overview of a sane backup strategy; You want *at least* two copies backed up. At least one of these should be stored in a geographically remote location. This should mitigate the probability of both copies being destroyed in the event of fire, flood, earthquake, metorite strike etc. The more locations you have backups the safer your data is.
Best practices is to use backup sets, in "father, son, grandfather" rotation. If you're serious about backups you'll have a daily, weekly and monthly set. At least two copies of. The rotation pattern is thus: Day one, backup to the father. Store at least one copy in a geographically remote location. Day two, backup to the son. Store at least one copy in georemote. Day three, backup to the grandfather. Store at least one copy georemote. Day four, backup to the father. Store at least one copy georemote. Day five, backup to the son of the daily sets, store at least one copy georemote. Backup to the father of the weekly set, store at least one georemote.
Repeat such a pattern for the weekly and the monthly sets. Should any one site be leveled then you've still multiple copies of the data. To assume somehow all three of the daily backups are invalid, then you've one from a week ago. two weeks ago. A month agow. two moneth ago etc. The probability of all copies becomming unusable(assuming stored well) are really really low – and get lower the more copies you have.
That may be a little much for most people – especially home users – but it gives you the largest chances of retrieving tangible data across the widest range of senario. If you really care for the data you'll make the effort – but some loose approximation of the above would likely be adequate.
There's many autonomous backup solutions. I like BackupPC. It's flexible, and backs up intelligently. One great feature is if I backup all my computers and they all have a file – test – and this file is the same on all machines, then it will only store one physical copy. Where it requires to store multiple copies of the same file, but with different contents, where possible it'll only save the difference between the two. Such cunning trickery can seriously impact the amount of space a backup requires, over more than one machine. The more machines you backup the more overall space you save.
Tho If you really want to protect yourself from malware – ransomware specifically – just get rid of winhoes. Anything else would be a good start. I'd suggest linux as most distro is free. There's millions of malware breeds and varients for winhoes – sometimes tens of thousands of new ones a month – but you can count the linux ones in the wild without running out of fingers. And even then they require(if it's used sensibly) your express permission in order to gain priviliges capable of impacting the system.
Should linux be something alien to you then you could do worse things than getting yourself a livedisc. Freely downloadable – typically as an .iso – commonly one would render bootable by either burning to optical or using some tool like unetbootin to place it on a USB stick or similar. Boot from fabricated media and you're away. Most live discs exist in RAM only, and don't mount internal storages as default so there should be no chance of causing accidental damages to the system by the attempt of trying it out. The entire OS will run happily like that. As it only exists in RAM, if you somehow manage to break it then a reboot should be all it takes to put it back. Once you've played with it enough to feel almost comfy in there, consider installing it. It'll run a lot faster. USB access speeds are quite low. But still significantly better than optical
For an introduction to linux I'd personally suggest linuxmint. The project has many goals which align with providing an easy to use environment out of the box. It boots with several things installed you're likely to recognise – like libre office, VLC, Firefox etc. Thusly provides for a reasonable range of functionality right off the bat. Should you feature difficulties, the preinstalled IRC client will, on opening, connect you to their support room which is typically manned 24/7. Based on ubuntu it dips into canoniocal's repositories – this is a large software stash giving you tens of thousands of things to install. All tried, tested and approved. No compiling or ostensible configurations.
One of linux's greatest strengths when it comes to avoiding malware is the permission structure. Winhoes has a permission struture too, but it's more of a formality. Malware commonly bypasse to elevate itself to the highest possible status(SYSTEM level. Sometimes with exploits over a decade old) at which point it can do as it pleases. I've not seen a linux infection in the wild that doesn't need permission – provided by input of pass to grant elevated privileges – in order to establish itself.
But wait! You're suggesting that people actually take responsibility for their computers and their usage. You're suggesting that they be mindful of the content that they view, double check URL addresses to ensure that the page they think they're visiting is actually on the site that should be hosting it. You're suggesting that we shouldn't install Java and Flash from anywhere else but Sun and Adobe. Outrageous!!!
We were happy being sheeple, and now you've gone and ruined it all. . .
If a noob get infected by Jigsaw there is a power switch at the back of the computer to instantly stop your machine (remove battery in laptop). Then use another computer to decrypt. Jigsaw is a program… does nothing without power :)
If there is a cure… power down your computer using a switch (instant power kill and not shutdown, so the Jigsaw cannot delete those 1000 files). Use another computer to decrypt files. Jigsaw is a program, it cannot delete files while it is not running :)
After powering down in such a situation, it's generally not a good idea to power it back up into the infected OS -=- Livediscs work wonders here as they allow an independant OS to load(also great to quickly diagnose if something not working is a hardware or software issue) and will readily provide somewhere to work for those who don't actually have multiple physical computers.
This ofc would require either having the presence of mind to burn a live before the event or access to another (library? etc) to fabricate one.
Operating retroactively isn't clever. Once the horse has left the stable closing the door doesn't matter anymore. Looking at a pile of HD's on fire and thinking "I wish I'd made backups" doesn't give you the same warm fuzzy feeling as looking at the same pile of HD's on fire and thinking "That's OK, I have backups".
Again, prevention is better than the cure. Deploy a hypervisor and container your browser. Now.
The browser is a gateway to executing code on your computer to the general public. Would you hang your car keys on a post next to your car so the general public can drive it about how and where they would like?
Modern malware is begining to commonly detect if it's in a VM and as this is how security researchers typically study it, then to throw them off the scent they don't exhibit the same behaviours in VM. Typically being entirely inert. Those that are not inert are limited in scope as to the damages it should be possible to cause.
A burning question I have (and difficult to prove without really knowing what you are doing) does virtualisation prevent this kind of encryption in the first place? Products like Comodo now provide a virtualised desktop to allow surfing that in theory prevents programs accessing the main hard drive to actually prevent this kind of encryption happening but it's just a theory at present. (a sandbox option) My own solution is to use an 80$ board with a DVD drive connected to it. I use firefox from a Linux CD (Mint or Ubuntu seem to work fine). Then I can surf until my hearts content, safely storing my DOC files on googles servers or other providers and have a completely clean installation every time for Banking, Shadow surfing or any other activity I want safe in the knowledge i'm free from worms. Ransom demanders. Keylogs. prying eyes (other than my own ISP, service provider, GHQ , Echelon and uncle tom cobbly) .