
An airport’s boarding gate displays leaked information that could have allowed attackers to gain access to passengers’ bookings and their personal details.
While waiting for his flight at an airport in Europe, Candid Wueest of Symantec’s security research team saw a timed-out web browser window on one of the boarding gate displays. Curious, he noted the window’s IP address and tried to open it on his smartphone.
To his surprise, Wueest opened up a screen showing not just what flights were leaving that particular gate but also what flights were leaving all gates across multiple airports via a single airline.
That’s not all he found, however, as Wueest explains in a blog post:
“On the public-facing server there was one page that immediately caught my eye. For each gate, there was a debug page available. The page listed all database fields with information available about the next flight. One of the queried tables was for passengers on the standby list. Various information about these passengers was listed including their complete booking reference codes, also known as passenger name record (PNR) locators.”
PNR locators are six-digit alphanumeric codes that are stored in the databases of airline computer reservation systems (CRS). Both airlines and airports use them to book a passenger’s flight. If someone can gain access to a PNR locator and the corresponding passenger’s last name, they can access passenger bookings for a flight through a particular airline.
Unfortunately, Wueest found passengers’ personal information using the debug pages displayed on his phone.
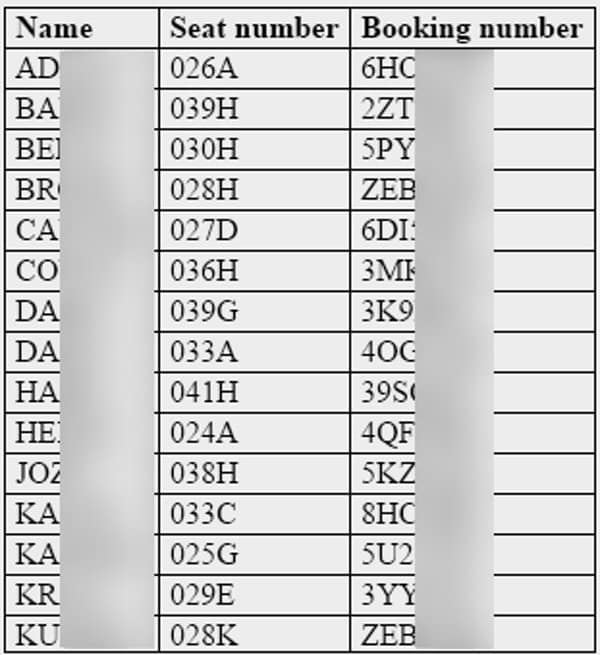
Most of the last names were shortened to about five characters. In some cases, he used those abbreviations to successfully guess passengers’ last names. For other passengers with four or five character last names, their full names were already revealed.
Using that information, an attacker could access a booking to see all the details of the flight and other passengers including their names, email addresses, dates of birth, and passport information (if an international flight). They could then abuse that information to commit all kinds of trouble.
The security researcher elaborates on that point:
“With most airlines, having the PNR code and passenger’s last name means an attacker can cancel the flight, rebook it for another date, or change customer details in their frequent flyer account. Basically, an attacker could gain full control over passenger bookings and have access to a lot of sensitive information that could also be used to carry out identity theft and phishing attacks.”
Wueest informed the airline of this issue, which has since been fixed. He also recommended the airline implement additional safeguards – such as CAPTCHAs, requesting additional information, and rate-limiting per IP address – to help protect passengers’ PNR codes against brute-force attacks.
But while this airline fixed the security hole, others might still be vulnerable. We therefore hope all airlines read Wueest’s report and take steps to better protect passengers’ PNR codes. That should include training all airport staff against social engineering attacks that try to trick them into giving up PNR locators.


